TeslaCrypt ransomware
In March 2015 a new type of ransomware affected thousands of users. Labeled as TeslaCrypt, the spiritual successor to Cryptolocker ransomware, encrypts over 180 different file types on victims computer and demands a payment for the decryption key.
How it works?
This ransomware affects all kinds of documents, databases, photographs, multimedia files as well as Steam or iTunes related files. All you will see is your file extension renamed to .ecc and a HELP_RESTORE_FILES.txt text file in each affected folder.
You will also see screen like the one below and you will know you are pretty screwed. But there is a chance you are amongst the few lucky ones that can recover their data.
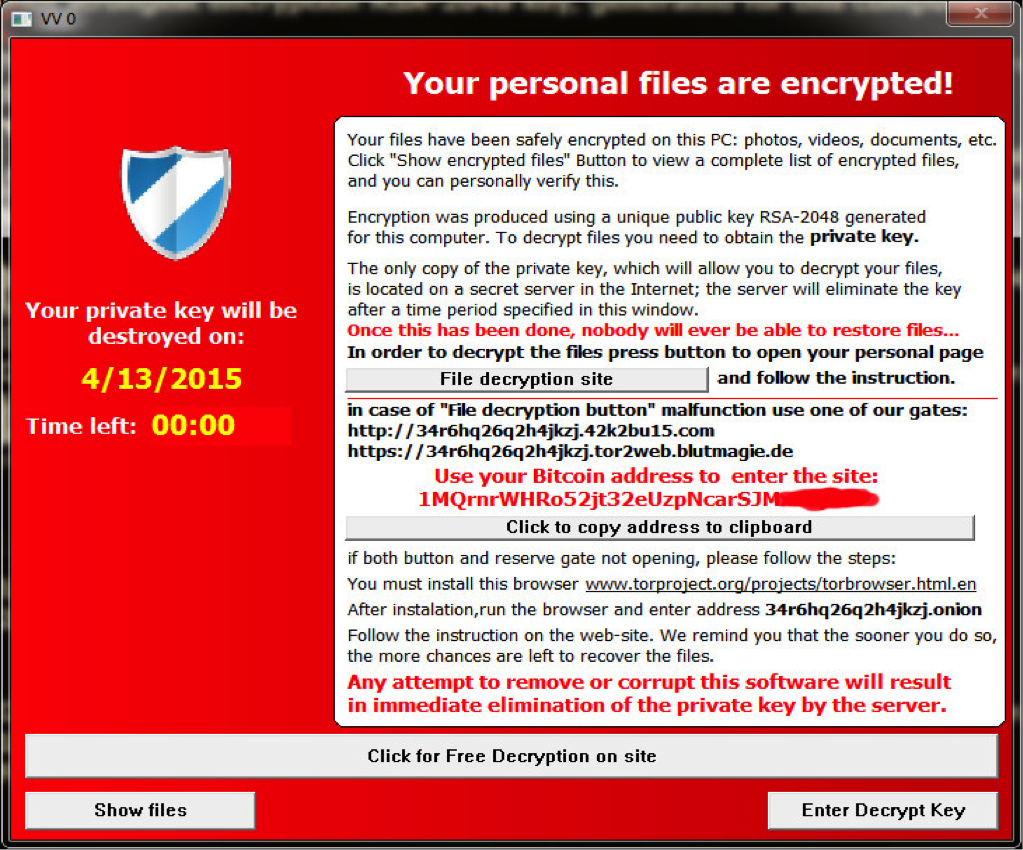
Although TeslaCrypt claims that it uses RSA-2048 asymmetric encryption algorithm, it in fact uses "just" AES symmetric one. Which is good because it means the same key is used for both encryption and decryption procedure. This enabled people at Cisco to develop a decryption tool. It is not perfect and does not always work, but it is at least partial success.
How it works? Well some version of the malware put a key.dat file in target machine and from this file a master key can be recovered. If you have no such file in your computer, you are still screwed. The technobabble around this is that the key.dat was already send to the ransomware server and that it is not that easy to generate a opposite effect.
TeslaCrypt decryption utility
You can download the TeslaCrypt decryption utility along with instructions from Cisco blogs. It is a command line utility available in three formats: Windows binary, a source for the Windows binary or a Python script.
Maybe future will bring some other utilities to reclaim your data, but for now your best protection is to perform regular backup of your crucial files.


